How To Set Up Mfa In Office 365
Keeping rail of your user's MFA Status is important to keep your tenant protected. For now, we can still use the Msol module for this in PowerShell, but Microsoft is planning to retire this module. And then I have recreated my successful MFA Status script with the Microsoft Graph module.
The Microsoft Graph module isn't fully completed yet. It doesn't just lack documentation, simply nosotros also can't retrieve all information all the same from it. For example, we can't retrieve (or set) the default MFA method with Graph at the moment.
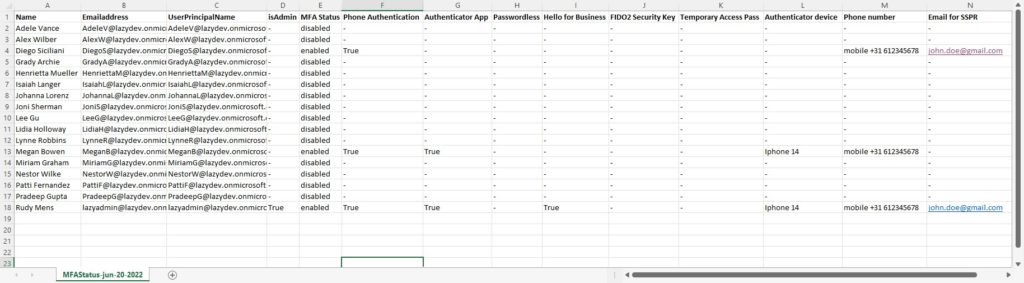
And then this new MFA Condition script can practice pretty much the aforementioned things as the old script:
- List the MFA Status of all users
- List configured MFA types for each user
- Go all the users that don't have MFA enabled
- Check the MFA status of a unmarried user
- Checks if a user is admin or not
- Go only the licensed and enabled users
But with Graph, we are besides able to call back a picayune bit more than data than with the old module. And so the following information is at present also retrieved:
- Authenticator device name
- Check if Hello for business is registered
- Registered electronic mail address for Cocky Services Password Reset (SSPR)
What nosotros currently can't retrieve is the default MFA method, and if MFA is enforced for the users (as in that the user needs to configure MFA the side by side fourth dimension after login).
As always, you volition discover the complete script at the end of the article.
Get MFA Status with Microsoft Graph and PowerShell
Microsoft Graph yet has a lot of features simply available in their beta release. So the outset thing the script does is connect to Graph with the required scopes and switch over to the beta profile. We can then retrieve all users with the Get-MgUser cmdlet.
Afterwards we have nerveless all the users we can use the Get-MgUserAuthenticationMethod cmdlet to become all the MFA details.
Requirements
Yous will need to have the Microsoft Graph module installed. The script will bank check if the module is installed, if not you will be given the option to install it.
Getting all users and their MFA Status
The script comes with a couple of parameters that we can use to fine-tune the export results. Just by default, it will get all licensed users, list the admins, and save the CSV Export at the same location equally the script. The script will open up the CSV file when completed.
So to get all users nosotros can but run the script:
# Get all licensed users: Get-MgMFAStatus.ps1
Go only users without MFA
When y'all have a big tenant yous probably only desire to see the users who don't take MFA enabled. To do this yous can add use the switch -withoutMFAOnly:
Become-MgMFAStatus.ps1 -withOutMFAOnly
Cheque MFA Condition of Admin simply
The script will list all admins by default, but you lot can as well check the MFA Status from admins only with the -adminsOnly switch:
Go-MgMFAStatus.ps1 -adminsOnly
Check the status of a specific user or a selection of users
It'south also possible to bank check the MFA condition of a specific user. We can specify the UserPrincipal proper noun of the user using the -UserPrincipalName parameter:
Get-MgMFAStatus -UserPrincipalName '[email protected]'
The parameter accepts a string array, so you tin comma separate the users that y'all want to recollect:
Get-MgMFAStatus -UserPrincipalName '[email protected]','[electronic mail protected]'
Another selection is to use the filter of the Get-MgUser cmdlet and so piping the Get-MgMFAStatus script:
Become-MgUser -Filter "country eq 'Netherlands'" | ForEach-Object { Become-MgMFAStatus -UserPrincipalName $_.UserPrincipalName } The Consummate Script
The complete script can exist downloaded from my Github repository, which I recommend using so y'all have always the latest version.
Tip
Quickly get the MFA Status of your users by adding a reference to the script in your PowerShell Contour. Read all about it in this article.
<# .Synopsis Become the MFA status for all users or a single user with Microsoft Graph .Clarification This script volition get the Azure MFA Status for your users. You can query all the users, admins simply or a single user. It will return the MFA Status, MFA type and registered devices. Note: Default MFA device is currently not supported https://docs.microsoft.com/en-us/graph/api/resources/authenticationmethods-overview?view=graph-rest-beta Hardwaretoken is not yet supported .NOTES Name: Get-MgMFAStatus Author: R. Mens - LazyAdmin.nl Version: 1.1 DateCreated: Jun 2022 Purpose/Change: Add Directory.Read.All telescopic .LINK https://lazyadmin.nl .EXAMPLE Get-MgMFAStatus Become the MFA Status of all enabled and licensed users and bank check if there are an admin or non .Instance Go-MgMFAStatus -UserPrincipalName '[email protected]','[electronic mail protected]' Go the MFA Status for the users John Doe and Jane Doe .Case Get-MgMFAStatus -withOutMFAOnly Become only the licensed and enabled users that don't have MFA enabled .Instance Get-MgMFAStatus -adminsOnly Get the MFA Status of the admins only .Case Get-MgUser -Filter "land eq 'Netherlands'" | ForEach-Object { Become-MgMFAStatus -UserPrincipalName $_.UserPrincipalName } Get the MFA status for all users in the Country The Netherlands. Yous can use a similar arroyo to run this for a department just. .EXAMPLE Go-MgMFAStatus -withOutMFAOnly| Export-CSV c:\temp\userwithoutmfa.csv -noTypeInformation Get all users without MFA and export them to a CSV file #> [CmdletBinding(DefaultParameterSetName="Default")] param( [Parameter( Mandatory = $imitation, ParameterSetName = "UserPrincipalName", HelpMessage = "Enter a unmarried UserPrincipalName or a comma separted list of UserPrincipalNames", Position = 0 )] [string[]]$UserPrincipalName, [Parameter( Mandatory = $false, ValueFromPipeline = $false, ParameterSetName = "AdminsOnly" )] # Get only the users that are an admin [switch]$adminsOnly = $false, [Parameter( Mandatory = $false, ValueFromPipeline = $fake, ParameterSetName = "Licensed" )] # Check only the MFA status of users that have license [switch]$IsLicensed = $true, [Parameter( Mandatory = $false, ValueFromPipeline = $true, ValueFromPipelineByPropertyName = $true, ParameterSetName = "withOutMFAOnly" )] # Get only the users that don't take MFA enabled [switch]$withOutMFAOnly = $false, [Parameter( Mandatory = $simulated, ValueFromPipeline = $false )] # Cheque if a user is an admin. Fix to $false to skip the check [switch]$listAdmins = $true, [Parameter( Mandatory = $false, HelpMessage = "Enter path to save the CSV file" )] [string]$path = ".\MFAStatus-$((Get-Date -format "MMM-dd-yyyy").ToString()).csv" ) Function ConnectTo-MgGraph { # Bank check if MS Graph module is installed if (-not(Get-InstalledModule Microsoft.Graph)) { Write-Host "Microsoft Graph module not found" -ForegroundColor Black -BackgroundColor Xanthous $install = Read-Host "Practice y'all want to install the Microsoft Graph Module?" if ($install -match "[yY]") { Install-Module Microsoft.Graph -Repository PSGallery -Scope CurrentUser -AllowClobber -Forcefulness }else{ Write-Host "Microsoft Graph module is required." -ForegroundColor Black -BackgroundColor Yellowish exit } } # Connect to Graph Write-Host "Connecting to Microsoft Graph" -ForegroundColor Cyan Connect-MgGraph -Scopes "User.Read.All, UserAuthenticationMethod.Read.All, Directory.Read.All" # Select the beta profile Select-MgProfile Beta } Function Get-Admins{ <# .SYNOPSIS Get all user with an Admin role #> process{ $admins = Get-MgDirectoryRole | Select-Object DisplayName, Id | %{$role = $_.displayName; Get-MgDirectoryRoleMember -DirectoryRoleId $_.id | where {$_.AdditionalProperties."@odata.blazon" -eq "#microsoft.graph.user"} | % {Get-MgUser -userid $_.id | Where-Object {($_.AssignedLicenses).count -gt 0}} } | Select @{Name="Role"; Expression = {$part}}, DisplayName, UserPrincipalName, Postal service, ObjectId | Sort-Object -Belongings Mail -Unique return $admins } } Function Get-Users { <# .SYNOPSIS Become users from the requested DN #> process{ # Set the properties to retrieve $select = @( 'id', 'DisplayName', 'userprincipalname', 'mail' ) $backdrop = $select + "AssignedLicenses" # Get enabled, disabled or both users switch ($enabled) { "true" {$filter = "AccountEnabled eq true and UserType eq 'member'"} "fake" {$filter = "AccountEnabled eq simulated and UserType eq 'member'"} "both" {$filter = "UserType eq 'member'"} } # Check if UserPrincipalName(s) are given if ($UserPrincipalName) { Write-host "Get users past proper name" -ForegroundColor Cyan $users = @() foreach ($user in $UserPrincipalName) { try { $users += Get-MgUser -UserId $user -Property $properties | select $select -ErrorAction Stop } grab { [PSCustomObject]@{ DisplayName = " - Not plant" UserPrincipalName = $User isAdmin = $null MFAEnabled = $null } } } }elseif($adminsOnly) { Write-host "Go admins only" -ForegroundColor Cyan $users = @() foreach ($admin in $admins) { $users += Get-MgUser -UserId $admin.UserPrincipalName -Belongings $backdrop | select $select } }else { if ($IsLicensed) { # Get only licensed users $users = Get-MgUser -Filter $filter -Holding $backdrop -all | Where-Object {($_.AssignedLicenses).count -gt 0} | select $select }else{ $users = Get-MgUser -Filter $filter -Belongings $properties -all | select $select } } return $users } } Function Go-MFAMethods { <# .SYNOPSIS Get the MFA status of the user #> param( [Parameter(Mandatory = $truthful)] $userId ) process{ # Become MFA details for each user [array]$mfaData = Get-MgUserAuthenticationMethod -UserId $userId # Create MFA details object $mfaMethods = [PSCustomObject][Ordered]@{ status = "-" authApp = "-" phoneAuth = "-" fido = "-" helloForBusiness = "-" emailAuth = "-" tempPass = "-" passwordLess = "-" softwareAuth = "-" authDevice = "-" authPhoneNr = "-" SSPREmail = "-" } ForEach ($method in $mfaData) { Switch ($method.AdditionalProperties["@odata.type"]) { "#microsoft.graph.microsoftAuthenticatorAuthenticationMethod" { # Microsoft Authenticator App $mfaMethods.authApp = $true $mfaMethods.authDevice = $method.AdditionalProperties["displayName"] $mfaMethods.status = "enabled" } "#microsoft.graph.phoneAuthenticationMethod" { # Phone authentication $mfaMethods.phoneAuth = $true $mfaMethods.authPhoneNr = $method.AdditionalProperties["phoneType", "phoneNumber"] -bring together ' ' $mfaMethods.status = "enabled" } "#microsoft.graph.fido2AuthenticationMethod" { # FIDO2 key $mfaMethods.fido = $true $fifoDetails = $method.AdditionalProperties["model"] $mfaMethods.status = "enabled" } "#microsoft.graph.passwordAuthenticationMethod" { # Countersign # When only the password is prepare, and so MFA is disabled. if ($mfaMethods.status -ne "enabled") {$mfaMethods.status = "disabled"} } "#microsoft.graph.windowsHelloForBusinessAuthenticationMethod" { # Windows Hello $mfaMethods.helloForBusiness = $truthful $helloForBusinessDetails = $method.AdditionalProperties["displayName"] $mfaMethods.status = "enabled" } "#microsoft.graph.emailAuthenticationMethod" { # Email Authentication $mfaMethods.emailAuth = $true $mfaMethods.SSPREmail = $method.AdditionalProperties["emailAddress"] $mfaMethods.condition = "enabled" } "microsoft.graph.temporaryAccessPassAuthenticationMethod" { # Temporary Access pass $mfaMethods.tempPass = $true $tempPassDetails = $method.AdditionalProperties["lifetimeInMinutes"] $mfaMethods.status = "enabled" } "#microsoft.graph.passwordlessMicrosoftAuthenticatorAuthenticationMethod" { # Passwordless $mfaMethods.passwordLess = $true $passwordLessDetails = $method.AdditionalProperties["displayName"] $mfaMethods.condition = "enabled" } "#microsoft.graph.softwareOathAuthenticationMethod" { # ThirdPartyAuthenticator $mfaMethods.softwareAuth = $true $mfaMethods.condition = "enabled" } } } Return $mfaMethods } } Function Get-MFAStatusUsers { <# .SYNOPSIS Get all Ad users #> process { Write-Host "Collecting users" -ForegroundColor Cyan # Collect users $users = Get-Users Write-Host "Processing" $users.count "users" -ForegroundColor Cyan # Collect and loop through all users $users | ForEach { $mfaMethods = Go-MFAMethods -userId $_.id if ($withOutMFAOnly) { if ($mfaMethods.status -eq "disabled") { [PSCustomObject]@{ "Name" = $_.DisplayName Emailaddress = $_.mail UserPrincipalName = $_.UserPrincipalName isAdmin = if ($listAdmins -and ($admins.UserPrincipalName -friction match $_.UserPrincipalName)) {$truthful} else {"-"} MFAEnabled = $faux "Phone number" = $mfaMethods.authPhoneNr "Email for SSPR" = $mfaMethods.SSPREmail } } }else{ [pscustomobject]@{ "Proper noun" = $_.DisplayName Emailaddress = $_.post UserPrincipalName = $_.UserPrincipalName isAdmin = if ($listAdmins -and ($admins.UserPrincipalName -lucifer $_.UserPrincipalName)) {$true} else {"-"} "MFA Status" = $mfaMethods.status # "MFA Default type" = "" - Non yet supported by MgGraph "Telephone Hallmark" = $mfaMethods.phoneAuth "Authenticator App" = $mfaMethods.authApp "Passwordless" = $mfaMethods.passwordLess "Hello for Business" = $mfaMethods.helloForBusiness "FIDO2 Security Central" = $mfaMethods.fido "Temporary Access Pass" = $mfaMethods.tempPass "Authenticator device" = $mfaMethods.authDevice "Phone number" = $mfaMethods.authPhoneNr "Electronic mail for SSPR" = $mfaMethods.SSPREmail } } } } } # Connect to Graph ConnectTo-MgGraph # Get Admins # Get all users with admin role $admins = $null if (($listAdmins) -or ($adminsOnly)) { $admins = Get-Admins } # Become MFA Status Get-MFAStatusUsers | Sort-Object Name | Consign-CSV -Path $path -NoTypeInformation if ((Get-Item $path).Length -gt 0) { Write-Host "Report finished and saved in $path" -ForegroundColor Light-green # Open the CSV file Invoke-Item $path }else{ Write-Host "Failed to create study" -ForegroundColor Red } Wrapping Upward
Having MFA enabled actually helps with protecting your tenant. This PowerShell script allows you to easily check the MFA condition of your users.
Make sure y'all also bank check this article with 20 other security tips for Office 365. You can find the Msol version of this script here.
If you constitute this script useful, then delight share information technology. If y'all have any questions then but driblet a comment below.
Yous may also similar 1 of the following PowerShell study scripts:
- Mailbox permissions report
- Mailbox size study
- OneDrive size report
Source: https://lazyadmin.nl/powershell/msgraph-mfa-status/

0 Response to "How To Set Up Mfa In Office 365"
Post a Comment